Reverse Engineering & Consulting Services
Identify Component Structure and Function at an Elemental Level
Identify Component Structure and Function at an Elemental Level
At the heart of GHB Intellect’s core competencies in the area of intellectual property is reverse engineering. Firstly, we have the capability to reverse engineer circuitry, software/firmware code, processes, systems, networks, and protocols. Secondly, hardware reverse engineering and reengineering are useful in designs if the original design architectures are unknown/lost or only partially available. The same is true for software reverse engineering for legacy software systems to complete incorrect or incomplete documentation.
Through tear-downs and reverse engineering, the discovery of the the original design of an object (software, hardware, protocol, network, etc.) or a process is attempted in order to duplicate or enhance the object/process or to prove infringement. Depending on the objective, the task can be (and often is) quite complicated. It requires a properly designed plan, the right set of labs and equipment, and the oversight of the subject matter experts to have a chance of success.
Most countries have regulations that make reverse engineering illegal for the purpose of stealing copyrighted or otherwise protected intellectual property. GHB Intellect takes intellectual property ownership very seriously and will not provide reverse engineering services when it is not legally permitted.
GHB Intellect uses highly specialized laboratories (Electronics, RF/Antenna, Electron Microscopy, Emulation, etc.) as well as state-of-the-art test equipment for reverse engineering purposes. Whether a chip-level circuit extraction, software/firmware extraction, or an air-interface protocol test is required, we have the tools and the know-how to pursue any required reverse engineering task.
Below we describe the various types of reverse engineering: Hardware, Software, Process, System, Network, Protocol. Make sure you also read GHB Intellect’s blog post on “What Goes Into Hardware Reverse Engineering” for more details about what is included in a hardware reverse engineering project.
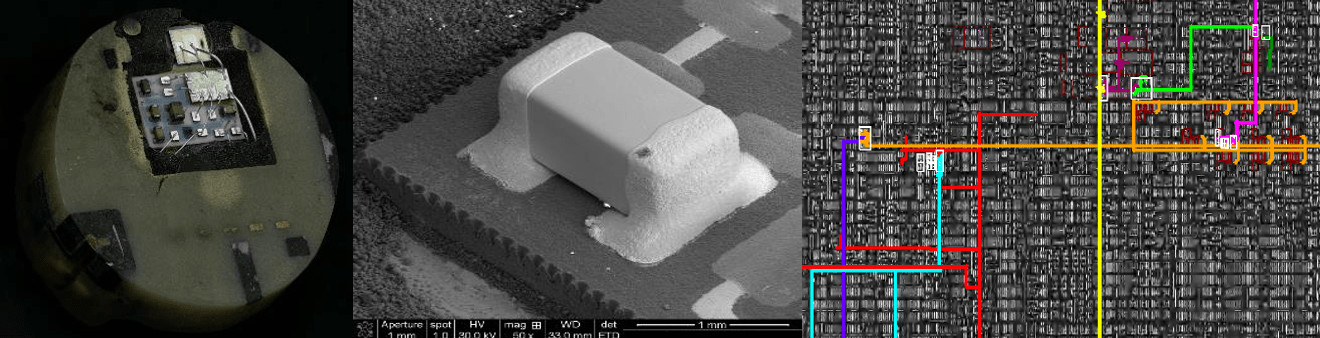
At the most basic level, hardware reverse engineering is performing a product teardown to see how it works. The teardown can start with the dismantling of the product into its individual components. Bill of material (BOM) can be generated based on the result. If the sough-after information is embedded in a PCB board, investigation of the board-level circuitry may be necessary. If design of interest is embedded inside an IC (Integrated Circuti) chip or an ASIC (Application Specific IC), then the task is much more complicated and requires chip-level investigations. GHB Intellect maintains the sought-after ability to investigate ICs (analog, digital, mixed signal) as well as their packaging. This is done in order to extract and analyze the embedded circuitry, or to gain insight on their manufacturing techniques. It typically involves decapping, cross-sectioning and high resolution SEM/TEM photography of the chip. If need be, it could also involve circuit extraction in all layers. All of the connections between the layers (vias) must be accounted for in order to build an accurate layout. The result of this work is compiled into a detailed circuit diagram.
After completion of the circuit diagram, our experts review the extracted circuits for quality assurance. All corrections and revisions are then made as necessary. Our experts then analyze the circuit and provide the required output in the context of the project at hand (IP infringement detection, design recovery, second sourcing, etc.)
We can also produce 3-D X-ray of manufactured parts or integrated circuit components. In these cases, we utilize a coordinate measuring machine (CMM) to measure the part. This produces a 3-D wire frame image that can be dimensioned for further inspection of intellectual property use.
We have extensive experience in determining how to cost-consciously approach specific engineering problems. This enhances our ability to keep the cost of such reverse engineering to a minimum while continuing to provide the utmost reliability to our clients.
In most cases, hardware reverse engineering requires an incredible amount of expertise and therefore must be performed by experts who have experience in efficiently performing the analyses. Otherwise, it can be quite expensive and the results may be unreliable. Read on about hardware reverse engineering examples.
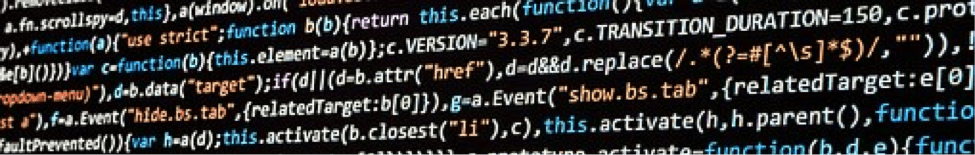
Software and firmware source code reverse engineering is another area in which GHB Intellect specializes. Software typically refers to higher-layer program typically run in microprocessors and CPUs. Firmware is a form of software that is inside an embedded and specialized processor that controls a system. Nearly every embedded electronic system includes some type of firmware code that is responsible for its control.
Software and firmware reverse engineering can refer to two main tasks, depending on the requirements of the project. First, access to the software/firmware code may need to be obtained, when the code is not readily available. This is commonly referred to as Code Extraction. Second, once the code is extracted, it needs to be interpreted to determine the underlying algorithms, formulas, protocols, etc. This sometimes is referred to as Code Review.
Sometimes, only the binary/machine code is accessible/available for a product. In such cases, the binary code needs to be disassembled to recover the original firmware or software. To disassemble a program, a software reverse engineer must choose the right tools for the desired outcome. The hexadecimal dumper is commonly used to display the embedded firmware in hexadecimal format. The disassembler is another tool that reads the binary code and presents the instructions in text form. However, a debugger is usually needed to compliment the disassembler because of its inability to separate instructions from data.
Our capabilities include accessing the software code at any layer, disassembling it, and then analyzing it as needed. This allows GHB Intellect to quickly and successfully detect any usage of specified intellectual property, which may be useful in an infringement litigation, But it is also helpful in non-litigation settings, for example:
Most software licenses specifically prohibit reverse engineering for the purpose of duplicating programs. These legal details are important in determining if undertaking the reverse engineering process is prudent.
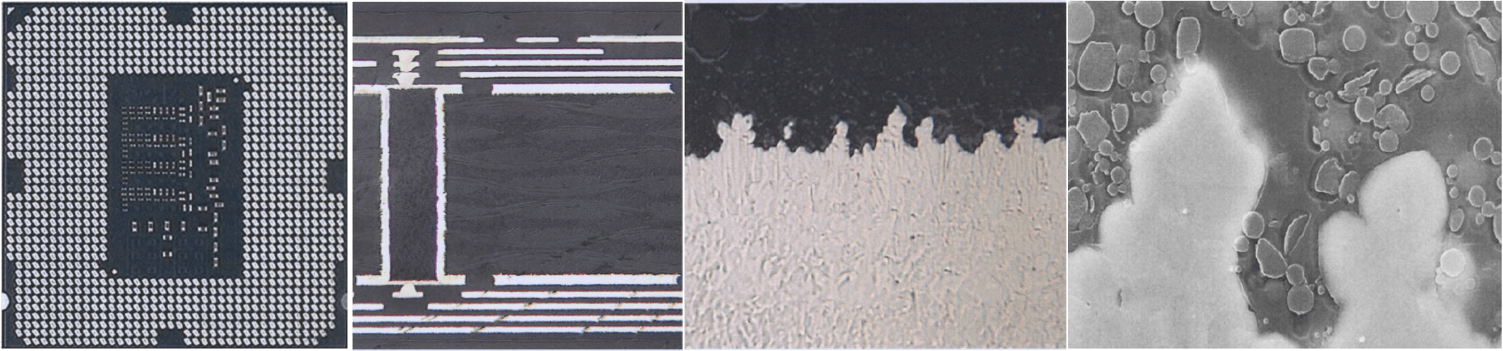
In addition to hardware and software reverse engineering, sometimes the question is on the process side of the product development. For example, the process of developing an integrated circuit or its packaging may be the central issue in a project. Or, the process and material associated with the development of a touchscreen sensor is to be discovered. In such cases, the chemical composition and the material deposition process may have to be investigated and reverse engineered.
Highly sophisticated laboratories, tools and equipment are typically necessary to enable a reliable process reverse engineering. GHB Intellect, with its state-of-the-art labs/equipment and its highly skilled technicians has extensive experiences in this area. As such, we can help develop and execute a reverse engineering plan that is both effective and cost-sensitive.
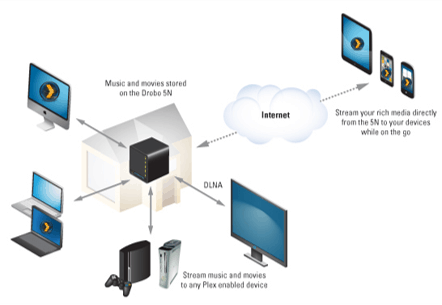
Other areas of expertise for GHB Intellect are at the system, network, and protocol level of reverse engineering. We are particularly adept at investigating embedded systems, which can be found inside a mobile phone, tablet, or other consumer electronics and communication devices. We frequently perform investigations for the following:
When inspecting wireless/mobile networks, drive testing the network may also be necessary. GHB Intellect has the ability to perform detailed analyses by utilizing state-of-the-art drive testing and data collection tools. We have the ability to dig deep into the Physical Layer (PHY), the MAC sub-layer (MAC), Data Link layer and the Network Layer (layers L1 through L3).
As mentioned above, there are many reasons to reverse engineer a product and many ways to do so. Hardware, software, process, system/network reverse engineering is an increasingly valuable area of expertise due to the intellectual property evidence that can be obtained in the process.
In a time of increasing capabilities and affordability, design engineers are able to create new products more quickly than ever before. It is important for reverse engineers to understand the complexities surrounding design engineering as well as reverse engineering.
Reverse engineering expertise in both software and hardware domains is especially necessary when the intellectual property of interest overlaps both areas, as is often the case with high-tech systems. Having highly experienced experts in both areas allows us to tackle such cases proficiently. Moreover, the project manager for the case makes sure that the various experts working on a project are well-coordinated and the final results and reports meet our stringent quality and consistency requirements. Our catalog of expert profiles is continuously expanding, and you can view some of their expertise areas in our expert profiles page.
GHB Intellect has been providing IP technical and business consulting services since 2007, including turn-key IP assessments, development, management, valuation, and monetization support. Our goal is to align our client’s IP portfolio development and monetization activities with their business objectives.
8380 Miramar Mall, Ste 224
San Diego, CA 92121
+1 (858) 367-3642
info@GHBintellect.com
HOURS
M-F: 9:00am – 5:00pm PST
S-Su: Closed
